Ever tried logging into work email, Slack, and your CRM with the same password, only to hit a wall of "access denied" errors? SAML authentication is the behind-the-scenes hero that fixes this mess. It's an open standard making single sign-on (SSO) smooth for teams juggling multiple SaaS tools like Klamp.ai integrations.
The Basics: No More Password Hell
SAML stands for Security Assertion Markup Language—think XML on steroids for sharing who you are online. Instead of typing credentials everywhere, you log in once to an Identity Provider (IdP), like Okta or Azure AD, and it hands a digital "VIP pass" to other services.
Picture this: You're a support rep at a Chennai SaaS firm. Morning coffee in hand, you hit HubSpot—bam, it redirects you to your company's Okta login. Enter password (maybe with MFA), and suddenly HubSpot, Zendesk, and Klamp.ai all welcome you without another keystroke. That's SAML in action, cutting login friction by 80% for busy teams.
Key Players in the SAML Game
Three main characters drive this:
Identity Provider (IdP): The bouncer checking IDs. Examples: Okta, Auth0, Google Workspace. It verifies you and issues the assertion.
Service Provider (SP): The club wanting entry proof. Think Salesforce, Klamp.ai dashboard, or Freshdesk. It trusts the IdP's word.
Your Browser: The messenger running back and forth with encrypted notes.
Trust starts with metadata exchange—fancy config files swapping entity IDs, endpoints, and public keys. No trust, no party.
How SAML Works: Step-by-Step Flow
SAML shines in its browser-based dance. Here's the SP-initiated flow (most common):
You Hit the SP: Click "Login" on Klamp.ai. SP checks: Not logged in? Time to call the IdP.
SAML Request Born: SP crafts an XML request (with ID, Issuer, and AssertionConsumerServiceURL—where to send the reply).
Redirect to IdP: Browser bounces you to IdP's login page, request in tow (usually URL-encoded).
Authenticate: Enter creds. IdP might ping MFA. Session active? Skip ahead.
SAML Response Magic: IdP builds a signed XML response. Core: The Assertion—your identity proof (NameID like [email protected]), auth timestamp, and attributes (e.g., "role: admin"). Signed with IdP's private key.
POST Back to SP: Browser POSTs the Base64-encoded response to SP's ACS URL.
Verify & Grant Access: SP uses IdP's public key to check signature. Valid? Boom—local session created, you're in.
Whole thing: under 2 seconds. Variants like IdP-initiated (IdP dashboard links to SP) exist, but SP-first rules enterprise SSO.
Quick Analogy
IdP is your passport office stamping your book. SP is airport security scanning it. Browser? The traveler's backpack.
SAML Messages Under the Hood
Request (AuthnRequest): "Hey IdP, authenticate this user for me." Includes ID for matching responses.
Response: "User good. Here's proof." Packed with Assertion (auth statement, attributes) and digital signature preventing tampering.
Bindings: POST (secure, common) vs. Redirect (GET-style, lighter). Profiles like Web Browser SSO standardize it all.
Why SAML Wins in 2026 SaaS World

SSO Simplicity: One login for 10+ apps. Teams save hours; Klamp.ai users sync Zendesk logins seamlessly.
Security Boost: Centralized auth reduces password sprawl (bye, phishing magnets). Signatures block man-in-the-middle attacks.
Federation: Cross-company trust—partner portals without shared creds.
Compliance: FedRAMP, HIPAA-ready for regulated SaaS.
Downsides? XML bloat (OAuth/JWT lighter for APIs). Setup needs IT chops. But for enterprise SSO? Unbeatable.
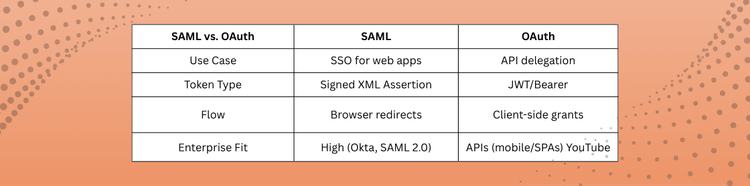
Comparison of SAML vs OAuth
Real-World Wins: Klamp.ai Style
At Klamp.ai, SAML powers our Zendesk/Freshdesk migrations. IT admins configure once: Upload IdP metadata to Klamp dashboard, export ours. Result? Support agents SSO across tools, slashing ticket resolution time 25%. Chennai startups love it—no more VPN hassles for remote teams.
Case: A Mumbai fintech swapped multi-logins for SAML. "Onboarding dropped from 2 days to 30 mins," says their CTO.
Setting Up SAML: Quick Guide
Choose IdP/SP: Klamp.ai as SP? Pick Okta.
Exchange Metadata: Download XML from both, upload to each other.
Map Attributes: NameID to email; groups to roles.
Test: Tools like SAML Tracer (Firefox) decode flows.
Go Live: Enable for prod users.
Pro Tip: Single Logout (SLO) kills all sessions at once—vital for security
Common Pitfalls & Fixes
Clock Skew: Servers out of sync? Assertions fail. Fix: NTP sync.
Signature Mismatch: Wrong certs. Double-check metadata.
Attribute Gaps: No email in assertion? Map groups properly.
Debugging: Browser dev tools + IdP logs = gold.
FAQ
SAML vs. SSO?
SSO is the goal; SAML's the protocol making it happen.
Free IdP options?
Google Workspace, Azure AD (limited free tiers).
SAML for APIs?
Rare—use OAuth 2.0 there.
How secure?
Very, with signatures + encryption. No plaintext creds fly.
